Sure enough a particular web page can tell you it takes you to a location of interest, but it’s not always true. Some links tend to redirect to unwanted or even harmful websites, or contain additional info. As such, Fast URL Checker comes with the means to help you inspect large lists of URLs.
Find out the safe way if links take you somewhere else
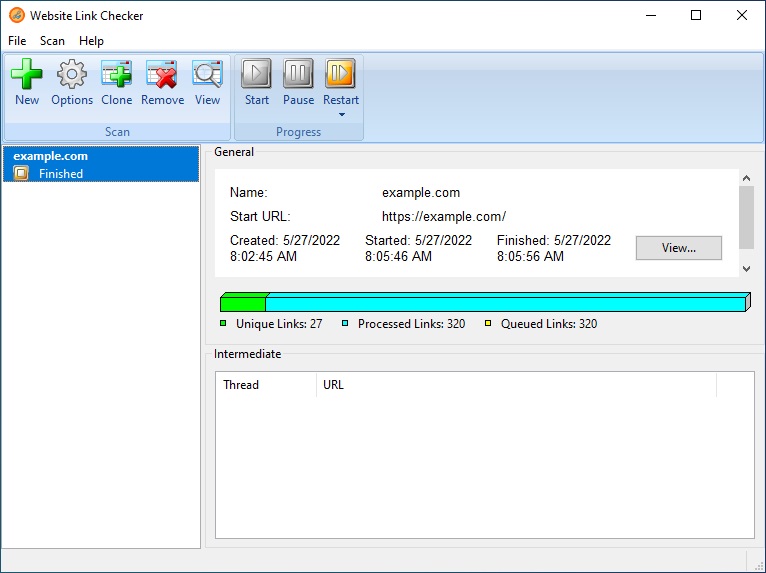
First of all, you might want to know that the application requires .NET Framework to function, which is usually delivered as a default feature in modern Windows iterations. You’re greeted by a clean interface, relying on classic window elements to display its features. Most of the space is where links and details are displayed, while the upper toolbar holds all necessary management functions.
The core function of the application is to reveal the truth behind links you provide. In other words, it verifies the status code, content type and its length, response time, redirects, relocations in between, and more. Multiple links can be checked at a time.
Filter lists and generate reports
First of all you need to add links to the operations. Since this isn’t done by filling in any fields in the application, you can either import them from files like TXT, HTML, CSV, or XML, from a previously saved report, or from clipboard with each URL on a different line.
The operation starts as soon as the links land in the application. Analysis doesn’t really take a lot of time, but it mostly depends on the complexity of the link, amount of provided URLs, as well as your Internet connection health or speed.
You can save the entire report or just redirects as CSV. Filters can be applied to match particular text strings, or simply by URL, response, type, status code, reason, size, and more. The options panel can be used to set speed, HTTP version, and user Agent.
A few last words
All things considered, we can state that Fast URL Checker is a neat way to tell if a website is clean or takes you to potentially malicious contents. Multiple URLs can be verified at a time, displaying all related info and redirects in an organized table you can save as report.
Fast URL Checker Crack+ With Full Keygen Free Download
Fast URL Checker Product Key is a neat tool that can help you find out if a website is safe or not. It offers a variety of ways to verify whether links you receive are dangerous. You can check multiple URLs at a time and get an accurate report.
Programmable robot fast / skippy fast detection of robots, spammers and robots detection and many more!
Fast URL Checker Activation Code is an awesome tool that can be helpful in filtering a list of web links. It can be used to check URLs for potential risks. The tool is a decent URL scanner that features several filters, such as specific text strings, HTTP versions, User Agents, etc.
Arbitrary code injection from anywhere in browser’s life
Bypass any browser sandbox
Run your own code as if it was executed on the victim’s browser
No special needs
Works with any file / URL (including HTTP, FTP, mailto, data:,…)
Didn’t require special privileges
How it works:
The key here is that this tool runs your code in the context of the victim’s web browser. That makes it impossible for the sandbox, such as CORS, to block the code. Since the code runs in the victim’s browser, the attacker also owns the victim’s browser.
Usually browser sandboxes, such as CORS, WAF, etc. only take effect in the HTTPS protocol. Once the code is injected, the attacker can make the HTTPS protocol less secure and intercept the traffic and get to the victim’s unencrypted traffic.
With this code injection tool, it’s impossible for the user to know that his browser is being hijacked by malicious code. And since this application is completely invisible to the user, it can’t be detected by WAF or any other protection systems.
Bypass sandbox
You can bypass the browser sandbox by defining the injection points as “local variables” and then “overwriting” them. For example, the injection could be to the “local variables” of the “onload” event handler of the “IFRAME” object.
To properly bypass the sandbox, you need to bind the injection points to the local variables. As soon as you bind the injection point to a local variable, the sandbox is no longer able to prevent the execution of the injected code.
That’s the power of the trick:
local variables can be easily defined at run time, so you can easily define the injection point. In fact, you don’t need to know anything about the function, you
Fast URL Checker Crack+ For PC Latest
1. Search criteria for a list of URLs from all selected protocols.
2. Search criteria for a list of URLs from selected protocols.
3. Filter URLs to get the lists.
4. Search for strings in the URL.
5. Filter URLs to get the lists.
6. Search for text strings in the URL.
7. Filter URLs to get the lists.
8. Search for digits in the URL.
9. Filter URLs to get the lists.
10. Search for email addresses in the URL.
11. Filter URLs to get the lists.
12. Search for credit card numbers in the URL.
13. Filter URLs to get the lists.
14. Search for IP address in the URL.
15. Filter URLs to get the lists.
16. Search for domain names in the URL.
17. Filter URLs to get the lists.
18. Search for hyperlink address in the URL.
19. Filter URLs to get the lists.
20. Extract URLs with specified text strings in the URL.
21. Extract URLs with specified text strings in the URL.
22. Extract URLs with specified text strings in the URL.
23. Extract URLs with specified text strings in the URL.
24. Extract URLs with specified text strings in the URL.
25. Extract URLs with specified text strings in the URL.
26. Extract URLs with specified text strings in the URL.
27. Extract URLs with specified text strings in the URL.
28. Extract URLs with specified text strings in the URL.
29. Extract URLs with specified text strings in the URL.
30. Extract URLs with specified text strings in the URL.
31. Extract URLs with specified text strings in the URL.
32. Extract URLs with specified text strings in the URL.
33. Extract URLs with specified text strings in the URL.
34. Extract URLs with specified text strings in the URL.
35. Extract URLs with specified text strings in the URL.
36. Extract URLs with specified text strings in the URL.
37. Extract URLs with specified text strings in the URL.
38. Extract URLs with specified text strings in the URL.
39. Extract URLs with specified text strings in the URL.
40. Extract URLs with specified text strings in the URL.
41. Extract URLs with specified text strings in the URL.
42. Extract URLs with specified text strings in the URL.
43. Extract URLs with specified
a86638bb04
Fast URL Checker Download
What’s New In Fast URL Checker?
When a website is created, all of its components are set up by the creation of a page file. If it is then copied from one server to another, all of the resources on the page will have to be copied over. In a large company, this can take a very long time. When a website is copy pasted over it will take longer and longer to load. And when the first user to visit the page comes along it will take a while to download the resources.
These days web hosting companies are typically very good at detecting if a website has been copied. So often they will simply refuse to host the new site and give you a message saying that your website has been illegally copied and will be removed from their servers. If you try and access the site, your browser will be redirected to the owner of the copy and message.
But there are some cases where you may not be able to detect if your website has been copy pasted and you may not know who has done it. This may happen with e-commerce sites where the original site has been shut down and the copies remain online. Or when a website has been copied to take advantage of any promotion, where the original site has been hijacked for promotion purposes.
If you want to check if your website has been copy pasted you need to find a way to tell if it has been copied. There are many ways of doing this. Some are very easy to do and some are a bit more complicated.
The easiest way is to use the file that is created when a website is created. This file can be accessed on all websites and is the reason that so many websites store files in the www directory on their server. If you were to copy the files from one website to another you would copy the directory that contains the files. So if you copied files from a real website to another you would copy the www directory.
When you have copied a directory the files will all have the same name and will all have the same contents. So if you copied the files for www.website1.com to www.website2.com you would copy the contents of www.website1.com and they would all have the same files. So if you were to check the files in the www directory for website2.com they would all have the same content. And this is a good way of checking to see if a website has been copy pasted.
This method is a good way of checking if a website has been copy pasted. But the biggest problem with this method is that if you are using a large number of servers it can take a very long time. And to do this you need to access each server. This is not a good way to do this if you have many servers because it can take a very long time.
A lot of people use a particular method to check to see if a website has been copy past
https://new.c.mi.com/ng/post/72055/Conan_The_Barbarian_Full_Movie_In_Hindi_Dubbed_NEW
https://new.c.mi.com/ng/post/70787/Summit_2_English_Book_Download_HOT
https://new.c.mi.com/my/post/460711/Himnos_Y_Coros_Idmji_Pdf_19_LINK
https://magic.ly/evexQsubyo
https://magic.ly/stigexclivgu/Watch-Online-Movie-A-Dishooml
https://new.c.mi.com/th/post/1336862/Boris_Brejcha_-_SAMPLES_WAV_EXCLUSIVE
https://new.c.mi.com/my/post/460392/Breaking_Bad_Season_S05_Complete_480p_BluRay_HDTV_
https://magic.ly/potiYtrabku/Ghost-Recon-Future-Soldier-Crack-Only-Skidrow-19-orVERIFIEDor
https://new.c.mi.com/ng/post/70661/Staad-pro-v8i-ss3-crack-download_LINK
https://new.c.mi.com/ng/post/72448/Manhunt_2_Crack_Reloaded_11_INSTALL
https://new.c.mi.com/th/post/1335981/Windows_7_Loader_Vista_Slic_Loader_248_X86andx64_R
https://new.c.mi.com/my/post/460323/TTSCepstralVoicesInclkeygen_HOT
https://new.c.mi.com/ng/post/70782/Image1_810x618_Png_PATCHED
System Requirements:
Processor: Intel® Core™ i7-2600K @ 3.4 GHz or above
Memory: 8 GB RAM
Graphics: NVIDIA GeForce GTX 970 4GB or higher
DirectX: Version 11
Storage: 17 GB available space
Additional Notes:
Available Windows 10, Windows 8/8.1, or Windows 7: Windows 10 is no longer available for Windows 7.L’Abordage de la Mémoire (Affrontement to Memory) is a group exhibition that explores human memory through artefacts recovered by underwater
https://maltymart.com/advert/virtual-programmable-keyboard-crack-free-download-updated-2022/
https://grxgloves.com/tadvtouchkeyboard-crack/
http://hshapparel.com/metro-wpf-2022/
https://kitchenwaresreview.com/excelindo-employee-attendance-calendar-lite-crack-activation-key/
https://aboutdance.com.ua/advert/hexonic-scantopdf-crack-activation-code-with-keygen-free-download-april-2022/
https://www.the-fox.it/2022/12/09/disko-ultimate-4317-crack-full-product-key-3264bit/
https://1w74.com/scrble-store-app-crack-torrent-activation-code-free-win-mac-2022-new/
https://hhinst.com/advert/clipname-1-2-3-crack-with-registration-code-3264bit/
https://www.prarthana.net/pra/50-movies-icon-pack-01-keygen-download-final-2022/
https://selfpowered.net/m3uforge-crack-with-license-code-free-x64-updated-2022/
